Throughout my career I’ve handled plenty of WordPress websites, tackling everything from malware recovery to bespoke customizations. In my free time, I do some freelance work on job portals helping…
Facebook Garage Sale Scam
Recently, I had a brush with an interesting scam on Facebook, specifically in the “Xbox Marketplace Singapore” group. A user going by “Ann Wong” posted a virtual garage sale, announcing…
Down The Rabbit Hole: Low-Cost PVC ID Card Printing
Introduction A few months ago, I needed to print some ID Cards, but local vendors quoted me a hefty S$10 per card, a price I wasn’t willing to pay for…
My “Lushious” Self-Care Bathtub
When I moved into my current house a few years ago, we did away with the bathtub in the guest bedroom’s bathroom (against my strong objections). The idea was so…
D’Wave Cabana at Wild Wild Wet
There is amazingly not a single image or description of the premium “D’Wave” Cabana over at Wild Wild Wet. Even the official website has no media of it. When I…
Enforcing a Claim under the Small Claims Tribunal
In November of 2019, a friend of mine (the “claimant”) was seeking legal remedies after being cheated of his rental deposit by a HDB flat owner (the “landlord”). After two…
Mitigating Banking Scams in Singapore
How often do people perform banking activities, or use the banking apps? Seldom enough to warrant some extra protections and caution around banking. Most people store their money in a…
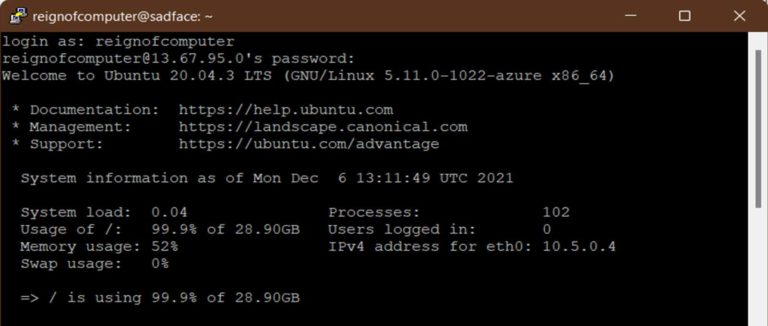
Resizing Out-of-Space Linux OS Disk on Microsoft Azure
Some weeks ago I awoke to one of my websites dead. A week before, I had upgraded the Virtual Machine’s MySQL from 5.6 to 8. More on that later. When…
NUS Greyhats WelcomeCTF 2021: Writeup
The National University of Singapore (NUS)’ Greyhats organized a WelcomeCTF from 13 to 15 August 2021. Interestingly, this CTF was sponsored by DSTA, who ran the ill-fated CDDC2021 just 2…